As all aspects of life have become increasingly digital, governments—and the European Union—have introduced digital identity schemes. These schemes replace physical ID cards with secure digital credentials (a login, app or digital wallet). Moreover, they often also support government verification of other claims (such as verifying your right to drive a vehicle without a physical driving license).
Proponents of digital identity say it can make everyday life simpler, reduce fraud and improve security. Stated benefits include speeding up bank account applications and proving your right to work instantly. It can also end “identity exclusion” for people who have the right to live and work in a country but lack the documents to prove it.
But the public response has shown that the general population is wary. Critics say that they fear state overreach, data misuse and surveillance. Recent IBM research shows that only 1 in 3 citizens have high trust in central governments, a sharp drop from pre-pandemic levels.
The world’s largest ID system, India’s Aadhaar, has over 1.3 billion users and has been in place since 2009, but it still faces protests. When the UK recently announced plans to introduce compulsory digital ID, a petition to Parliament titled “Do not introduce digital ID cards” quickly gained 2.8 million signatures.
The “privacy paradox” we first identified in 2008 comes into play here: technology has the power to both empower citizens as well as control them. Seventeen years later, the question remains: how can governments build an effective digital identity infrastructure while also earning public trust?
The key lies in creating a system that people believe in, not just comply with; one that is built for broad acceptance, human-centred and secure. Read on to learn how.
Be accepted: Build on familiarity and integrate open standards
To create a system that people are willing to trust, adopt technologies and processes that are already in use. Smartphone wallets and face authentication feel natural to the millions that use them daily. Familiarity builds confidence and drives adoption.
Build on existing initiatives, for example national single sign-on for digital government services, such as the UK’s GOV.UK One Login. Integrate existing processes, data and systems, rather than creating new silos; use open standards, such as verifiable credentials. Integrated standards-based solutions accelerate adoption, provide flexibility and improve value for money.
Learn from success stories. Estonia’s digital identity system covers 99% of citizens, supports digital and traditional processes and enables everything from voting to banking. Australia’s digital ID allows people to prove their identity from their device without physical documents. This feature makes it easier and quicker to request a tax file number or apply to rent a property. The UK has nearly fifty private sector organizations that are registered as identity providers under its digital identity and attributes trust framework.
Be human-centred: Put people first
Start with the individual, not the system. Digital identity must give people control over their data, letting them decide what to share and with whom. Ensure that people can see who has accessed their data and why—like Estonians can with their digital ID. We described in recent reports on digital identity how this feature can be achieved with digital credentials in the public and private sectors.
Consider applying techniques such as selective disclosure, zero-knowledge proofs and potentially even anonymous binding and standards like Solid, which put the user in control and allow verification without revealing unnecessary information. Think of it like showing a shop that you’re old enough to buy age-restricted products without revealing your date of birth, name or address.
Design for inclusivity: support people without smartphones by providing face-to-face enrollment options. Moreover, co-create the system with civil society and industry using open, transparent processes designed for the digital era.
Be secure: Protect trust from day one
A widely used digital identity system is a piece of critical national infrastructure that underpins essential services, making it a prime target for cyberattacks. Without it, people cannot identify themselves when accessing government or private-sector services, causing daily life to not function normally. One major breach could erase trust overnight.
Security must be embedded from the start. Public key encryption can provide confidentiality and integrity; the same way it secures online payments. Employ a decentralized architecture to avoid a single point of failure. It helps keep the scheme operational even if one of its systems is compromised, while also avoiding other risks inherent in creating another new, centralized, government database.
Incorporate leading identity fraud controls and robust easy to use processes for keeping data accurate—taking inspiration from industries like banking.
Resolve the paradox
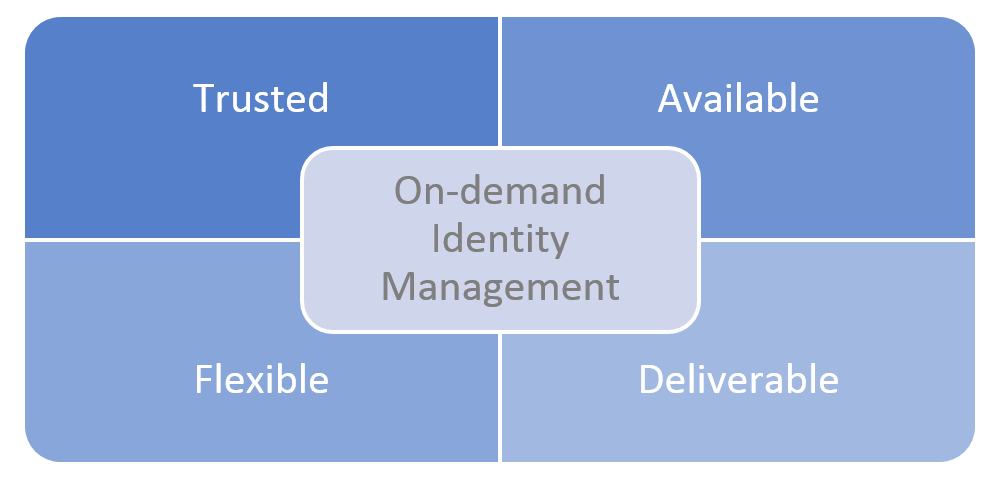
Governments now have the tools to move beyond the privacy paradox and create privacy respecting secure digital ID. This ID can be downloaded to an individual’s smartphone and instantly verifies their right to drive, work, buy age-restricted items or any other government attested claim about them.
By creating flexible, human-centred and secure processes, built on the foundations they already have, they can create an identity infrastructure that serves governments, business and citizens, for decades to come.
]]>